
Security analysts attribute the activity to FDN3 (AS211736), which is controlled by FOP Dmytro Nedilskyi, and which spearheaded several hundred thousand login attempts over a concentrated three-day period.
Intelligence suggests that FDN3 operates within a broader abusive infrastructure alongside VAIZ-AS (AS61432), ERISHENNYA-ASN (AS210950), and Seychelles-based TK-NET (AS210848), all of which were announced in August 2021 and frequently exchange IPv4 prefixes to evade blocklisting.
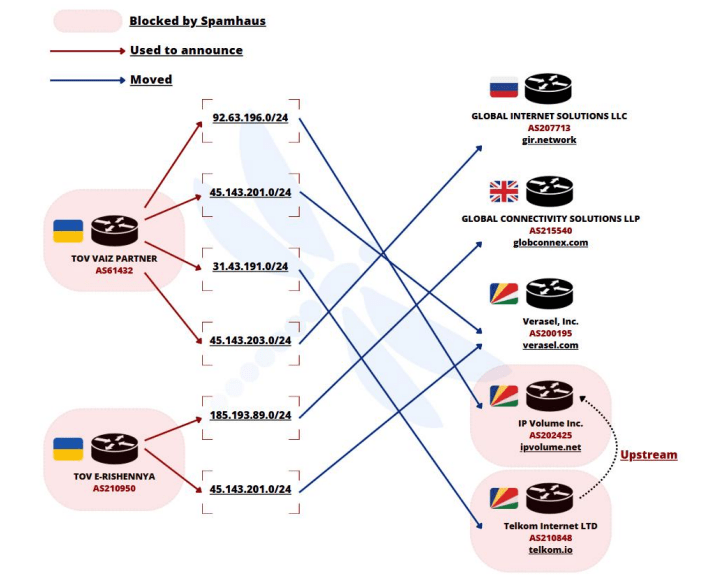
These prefix exchanges enable the threat actors to rapidly shift their attack infrastructure when individual networks are sinkholed or blacklisted.
For example, prefixes originally advertised by VAIZ-AS were later re-announced by ERISHENNYA-ASN and TK-NET, only to resume the same high-volume credential-guessing operations against corporate VPN concentrators and remote desktop services. Observed attack patterns include:
- Credential lists: Utilization of large, known password lists combined with spray-friendly timing to avoid lockout thresholds.
- Login protocols: Targeting both RDP port 3389 and SSL VPN portals over TCP ports 443 and 8443.
- Attack velocity: Sustained bursts of 5,000–10,000 attempts per hour from changing prefixes, maintaining continuous pressure.
Notably, prefix swaps also involve “IP Volume Inc.” (AS202425). This Seychelles-based entity serves as a front for Ecatel, which acts as the primary transit provider for a significant portion of the abusive network.

and originating from AS202425 in April 2025.
Concurrently, U.S.-registered bulletproof hoster KPROHOST LLC (AS214940) under Virtualine management has been observed exchanging prefixes with FDN3, suggesting a single administrative entity orchestrating infrastructure migrations to frustrate attribution and defenses.
Infrastructure Hijinks – Evasive Infrastructure and Partnership
Investigators with Intrinsec Cyber Threat Intelligence (CTI) report a high confidence linkage among these ASNs, supported by:
- Simultaneous spikes in attack volume across multiple prefix re-announcements.
- Identical attack signatures such as standard User-Agent strings and login failure response patterns—regardless of originating ASN.
- Shared upstream transit through Ecatel’s IP Volume Inc., indicating reliance on bulletproof transit for anonymized launching points.

These findings imply not only a robust technical playbook for evading network defenses but also strong partnerships with bulletproof hosting providers willing to overlook abuse complaints. The agile network reconfiguration suggests a central administrator with intimate access to routing registry operations.
Proactive Defense – Leveraging Intrinsec’s CTI Services
To combat these evolving threats, organizations must adopt proactive detection and response strategies.
Intrinsec’s CTI services combine data from SOC, MDR, and CERT-Intrinsec incident response teams with bespoke threat hunting, honeypots, and reverse-engineering. Key offerings include:
- Risk anticipation feeds from IOCs, fully TIP-compliant, to adapt EDR, XDR, and SIEM rules in real time.
- Digital risk monitoring for data leak detection, external asset discovery, and brand protection.
Early integration of high-value intelligence into enforcement platforms can mitigate credential-based attacks before compromise, ensuring continuous adaptation against this agile, prefix-hopping adversary.
Find this Story Interesting! Follow us on Google News , LinkedIn and X to Get More Instant Updates
The post Critical Alert – Ukrainian Attackers Intensify Brute-Force and Password-Spraying Assaults on SSL VPNs and RDP Gateways appeared first on Cyber Security News.
Discover more from RSS Feeds Cloud
Subscribe to get the latest posts sent to your email.

