Cybercriminals continue to adapt their tactics, taking advantage of the very tools and platforms organizations rely on every day. From trusted digital signature services to mobile apps and browser extensions, attackers are finding creative ways to blend malicious activity into normal business workflows. The result is a threat landscape where familiar tools can become unexpected entry points.
The encouraging news is that these attacks follow patterns. Once you understand how they work, you can spot them sooner, train your users more effectively, and put the right safeguards in place to stop them before they escalate.
This month at CyberHoot, we’re examining four developments that highlight how attackers are evolving their methods while targeting the same fundamental weaknesses: trust, convenience, and common human behaviors.
Cybercriminals continue to exploit DocuSign by using highly customizable phishing templates that closely mimic legitimate document notifications. These messages appear authentic, are common enough not to raise suspicions, and often urgent, making them particularly effective at tricking users into handing over credentials or sensitive information. We’ll walk through how these campaigns operate and what signals your team should watch for before interacting with document signature requests.
A new Android malware strain called PromptSpy is raising eyebrows given its unusual capability: it covertly co-opts an AI assistant to generate convincing phishing messages and tailor malicious activity. By feeding the AI benign-looking prompts, it tricks a normally helpful system into unknowingly supporting hacker attacks. This blending of malware and AI-driven automation signals a new level of sophistication that security teams must be aware of.
Ransomware is also evolving. Rather than relying solely on traditional attack vectors, many operators are shifting toward newer entry points such as compromised credentials, exposed services, and third-party access. Understanding where attackers are gaining their initial foothold is key to strengthening your defenses before encryption ransoms ever begin.
Finally, a malicious Chrome extension posing as a legitimate business productivity tool is quietly harvesting sensitive data from unsuspecting users. Initial reports came from distant corners of the internet, however, given early success these attacks are sure to spread. Browser-based attacks like this are particularly dangerous because they operate inside trusted environments and often bypass traditional perimeter defenses.
Each of these threats reinforces a simple reality: modern attacks rarely look obviously malicious. They succeed because they resemble normal business activity. They play on end user proclivities.
Read on to learn how these threats work, what they mean for your organization, and the practical steps you can take to stay ahead of them.
Craig
CEO, Co-Founder CyberHoot
Cybercriminals Are Exploiting DocuSign with Customizable Phishing Templates

PromptSpy: The Android Malware That Hired an AI Assistant

Ransomware Entry Points are Changing. Here Is What to Know and What To Do About It?

Malicious Chrome Extension Disguised as a Business Tools

vCISO Corner
In this month’s vCISO Corner, Dave Stacy, CISSP, FLMI, shares insights on the recent increase in hacker activity tied to the ongoing conflict in the Middle East and what organizations should be watching for. His advisory highlights why these events tend to trigger spikes in cyber threats and outlines practical steps businesses can take to strengthen their defenses.
Increased Hacker Activity Due to Middle East Conflict
Given the evolving Middle East situation, I advise you to be extra vigilant and maintain high situational awareness regarding the protection of Company information assets. We have already seen one major attack on a US company (Stryker) that caused significant business disruption and data loss when a large volume of data was “wiped” from thousands of Stryker devices. Reportedly, over 50,000 employees were asked to disconnect from all networks and avoid turning on their company devices.
Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. A trusted source with knowledge of the Stryker attack, speaking on condition of anonymity, told KrebsOnSecurity that the perpetrators in this case appear to have used Microsoft Intune to issue a ‘remote wipe’ command against all connected devices. Further, it appears the attackers may have obtained a privileged Intune system administrator account via a successful phishing operation to launch this attack. Iran has claimed responsibility for the attack, stating it was in retaliation for U.S. military action against their country.
I think it’s likely we’re going to see more attacks like this from Iranian hackers and their sympathizers, as well as from opportunists who will try to take advantage of the chaos and confusion. While the mainstream media focuses on the traditional manifestations of military conflict (e.g., ships, planes, bombs, missiles, etc.), cyberspace is likely to become a new “front” for attacks against government and commercial networks in the U.S. and allied countries. The objective is to create chaos and inflict financial hardship. In my opinion, no organization is immune from this threat.
In this environment, your best course of action is to:
- Communicate with your employees and ask them to be especially vigilant regarding phishing attempts and other forms of social engineering.
- Ensure that your system administrators are using individually assigned accounts that require multi-factor authentication and that they have a separate account for non-system-administrative work tasks.
- Review your back-up procedures and ensure that you have immutable back-ups that are “air-gapped” from your primary network.
- Review your incident response plan and keep it handy. Discuss business contingencies with your executive leaders in the event that you need to tell your users to disconnect from the network and turn off their devices.
- Keep abreast of evolving threats by seeking out credible sources of information. One source I’ve found to be very helpful, and not “alarmist,” is KrebsonSecurity.

Dave Stacy, CISSP, FLMI
vCISO
Customer Spotlight
Liking CyberHoot? We need your help. Please leave us a review using the links below!
TrustPilot.com | G2.com | Capterra.com | Google.com | TrustRadius.com | Gartner.com
– G2
For more information on how to leave a CyberHoot review, please watch the brief video overviews below. Note: to avoid fraudulent reviews, each review website will require to you to create and validate your identity through an email account registration process.
- How to leave a TrustPilot Review
- How to leave a G2 Review
- How to write a Capterra.com Review
- How to write a Google Review of CyberHoot
- How to leave a TrustRadius Review
- How to leave us a Gartner ‘Peer Review’ Review
CyberHoot Awarded Badges from G2

Cybersecurity Term of the Month:
Vector Database / Vector Store
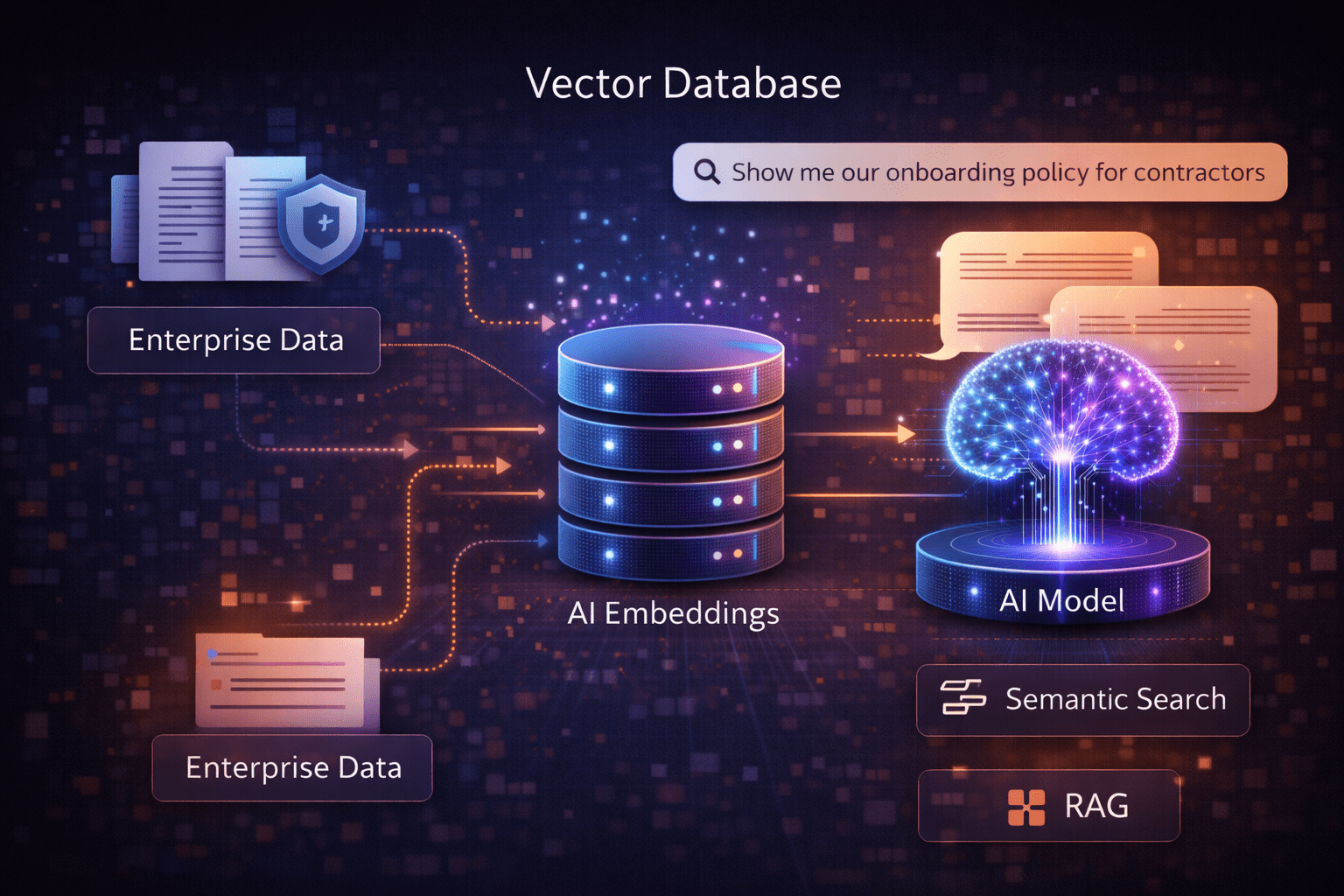
A vector database, also called a vector store, is a specialized data system designed to store and search vector embeddings, which are numerical representations of text, images, or other data created by machine learning models. These embeddings capture semantic meaning, allowing systems to find information based on similarity, not exact keywords.
Vector databases are a core component of modern AI systems, especially those using semantic search and Retrieval-Augmented Generation (RAG). Instead of asking “does this document contain these words,” the system asks “which documents are most similar in meaning to this question.”
Recently Added Features
Power Platform Release Notes
- Added ability to restore non local user and set it to local in archive table and mass actions.
- Added logging for Azure and Google sync setting updates.
- Added celebration popup with confetti when user moves up in Hoot Rank or passes an assignment.
- Renamed MSP Settings to Site Settings.
- Added ability to drag and move popover in HootPhish.
- Added measures to reduce AttackPhish false positives in live campaigns.
- Updated Leaderboard Ordering to sort by rank.
Autopilot Platform Release Notes
- Redesigned HootPhish Challenge results page in Autopilot to show more information/metrics on the challenge.
- Added ability to restore sync user as local.
- Added send emails from/branding override option in customer edit and add modal.
- Added CSV export button to custom hoot library tables.
- Added celebration popup with confetti when user moves up in Hoot Rank or passes an assignment.
- Renamed MSP Settings to Site Settings.
- Added ability to drag popover in HootPhish.
- Added Tenant and site logs page and API Documentation
- Added measures to reduce AttackPhish false positives.
- Updated CustomHoots to assign all active assignments to users in the assigned groups, rather than only assignments created in past day since user was created.
- Updated Leaderboard Ordering to sort by rank.
Check out Craig Taylor, CEO and Co-Founder of CyberHoot, Featured on the In Talk To Th3 Doc Podcast!
New Feature Alert: Custom AttackPhish

We’re excited to introduce Custom AttackPhish, a new feature within CyberHoot’s Autopilot platform that gives administrators greater flexibility when running phishing simulations. With Custom AttackPhish, (located in our CustomHoots Power-Up) admins can create and launch customized phishing campaigns that better reflect the real-world threats their users may encounter.
This helps organizations deliver more relevant security awareness training while improving users’ ability to recognize and respond to phishing attempts.
If you need additional help, you can always reach our support team at support@cyberhoot.com.

Enroll in CyberHoot’s Referral Program today and start earning a 20% share of all revenue generated for one year by those who register through your exclusive referral link. As a referral partner, not only will you receive financial rewards, but you’ll also experience the satisfaction of aiding others in becoming more security-conscious, safeguarding them against cyber threats. Don’t hesitate, sign up now at https://cyberhoot.com/referral-program/.
Referral through Autopilot’s Dashboard:
Join CyberHoot in our mission to create a more aware and better secured world! Recommend CyberHoot Autopilot to a friend, and they will enjoy a complimentary first month. For every new sign up who uses your referral link, you will receive a free month added to your account. This offer is exclusively for first-time CyberHoot registrants.

CyberHoot has Free Cybersecurity Training for Individuals
Know someone who had a close call recently with a cyber attack, phishing email, or social engineering phone call? Recommend CyberHoot’s free cybersecurity training. They’ll receive six (6) videos (each video is 3-4min.) and one of our positive reinforcement, hyper-realistic, phishing simulations. All for free.
Registration: https://cyberhoot.com/individuals
Looking for additional resources?
CyberHoot White Paper Download – How HootPhish Improves upon AttackPhish
All New: 2025 Infographics on Cybersecurity Statistics
Secure your business with CyberHoot Today!!!
The post CyberHoot’s Cybersecurity Newsletter: March 2026 appeared first on CyberHoot.
Discover more from RSS Feeds Cloud
Subscribe to get the latest posts sent to your email.